In the era of ChatGPT, Gemini, and Claude, copying and pasting data to solve problems has become a habit. However, behind this convenience is a huge security risk. Data Masking is no longer just an option; it is a vital skill to protect your career and your company’s reputation.
1. The Temptation and the "AI Trap"
Many employees copy-paste error logs or customer emails into AI to get fast results. The danger is that AI learns from this data and might accidentally reveal it to other users later.
According to security experts, the Samsung data leak (where engineers pasted secret code into ChatGPT) is a big lesson. At ISB Vietnam, we believe Data Masking is a mandatory skill before you hit "Enter" on any AI tool.
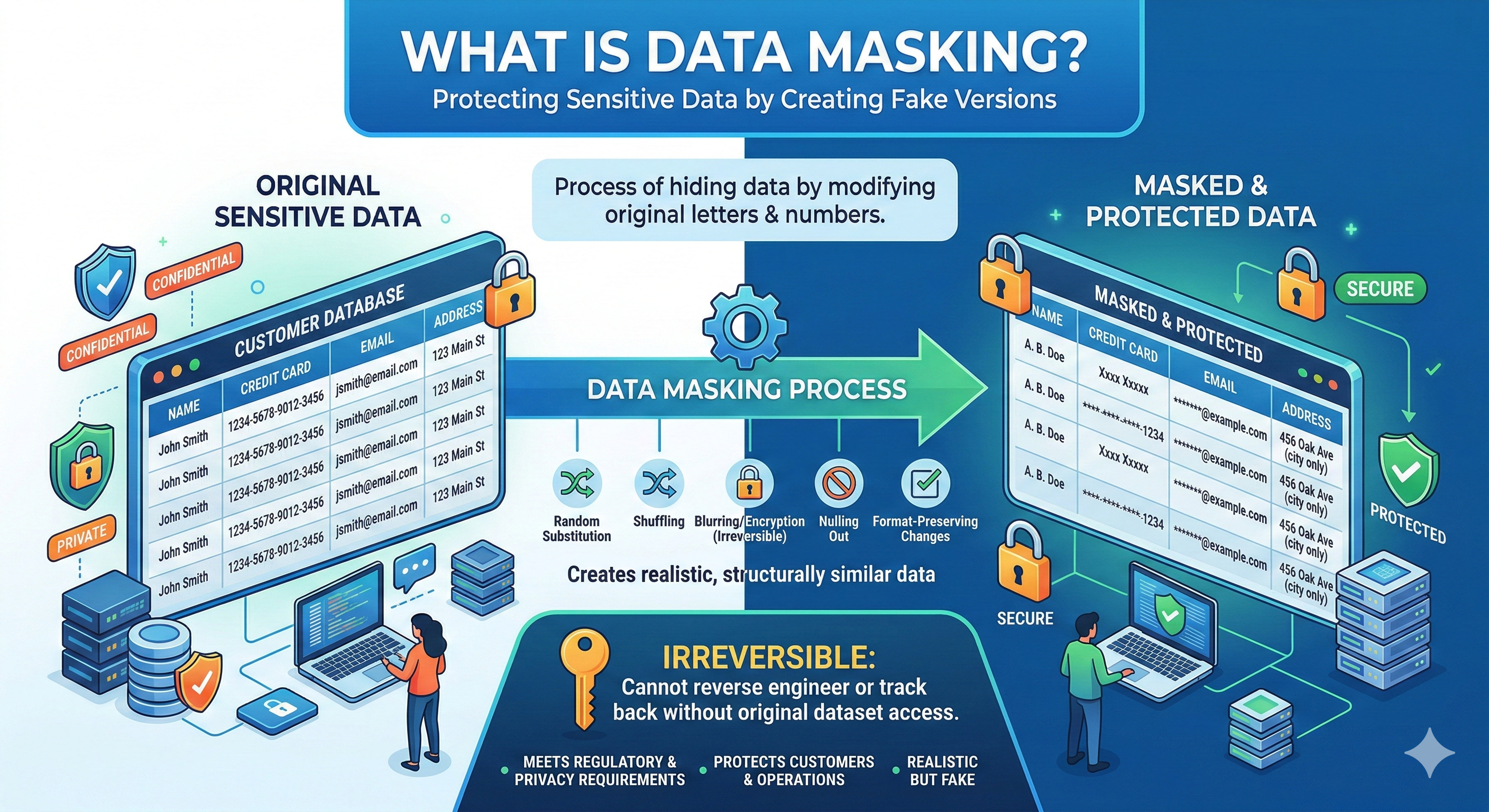
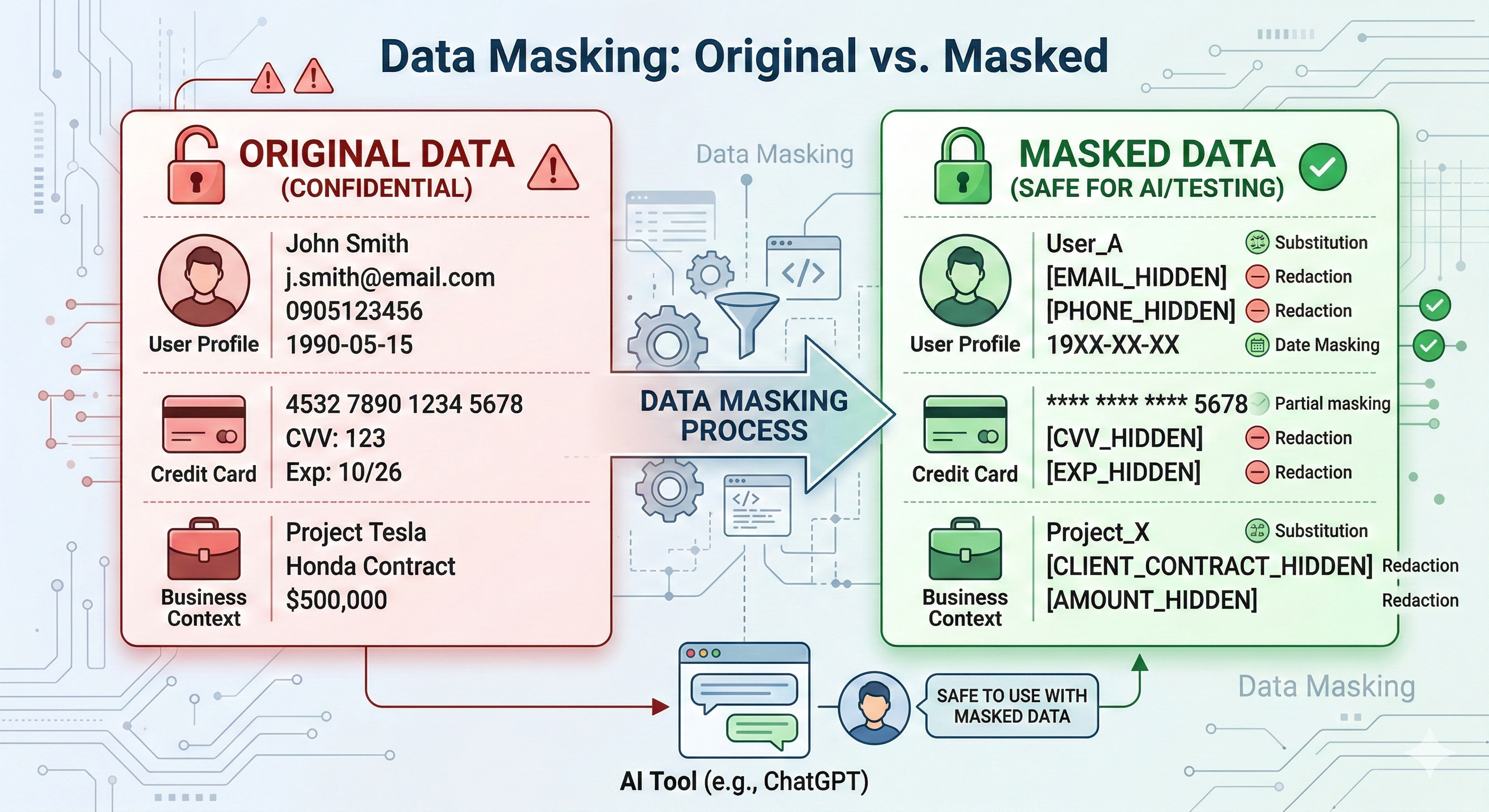
2. What is Data Masking?
Data Masking is the process of hiding sensitive data by changing original letters and numbers.
The goal is to create a "fake" version of the data that keeps the same structure. This way, the AI can still understand the logic and fix the error, but it won't know the real identity of the person or the business.
3. The "Danger Zone": 6 Types of Data You Must Never Paste
Before talking to AI, check this list and mask these items:
|
No. |
Data Type |
What’s Included (Examples) |
|
1 |
Personally Identifiable Info (PII) |
Full names, addresses, phone numbers, ID/Passport numbers, personal emails. |
|
2 |
Financial & Banking Data |
Credit card numbers, bank accounts, transaction history, payment credentials. |
|
3 |
Trade Secrets & Business Info |
Proprietary algorithms, strategic plans, upcoming product specifications. |
|
4 |
Biometric Data |
Fingerprints, facial recognition, retina scans, voiceprints. |
|
5 |
Medical & Health Records |
Patient histories, prescriptions, diagnostic details, health insurance info. |
|
6 |
Private Ideas & IP |
Unpublished research, confidential brainstorming, creative intellectual property. |
4. Practical Data Masking Techniques
A. Popular Data Masking Techniques
|
Method |
How it works |
Best used for |
|
Substitution |
Replaces real data with similar but fake values (e.g., replace a real name with a name from a random list). |
Names, Credit card numbers. |
|
Randomization |
Replaces sensitive data with totally random values that have no connection to the original. |
Addresses, PII. |
|
Shuffling |
Mixes the values within the same column. The data is real, but it now belongs to the wrong records. |
Maintaining statistical relationships. |
|
Encryption |
Uses algorithms to turn data into an unreadable format. Only people with a "key" can read it. |
High-level security (but can slow down analysis). |
|
Hashing |
Converts data into a fixed-length string of random characters. It cannot be reversed. |
Passwords or data verification. |
|
Tokenization |
Replaces data with a "token" (reference value). The real data is stored in a separate, secure vault. |
Sensitive production data & Compliance. |
|
Nulling (Blanking) |
Replaces data with a "null" value or a blank space. It simply removes the information. |
Removing data while keeping the format. |
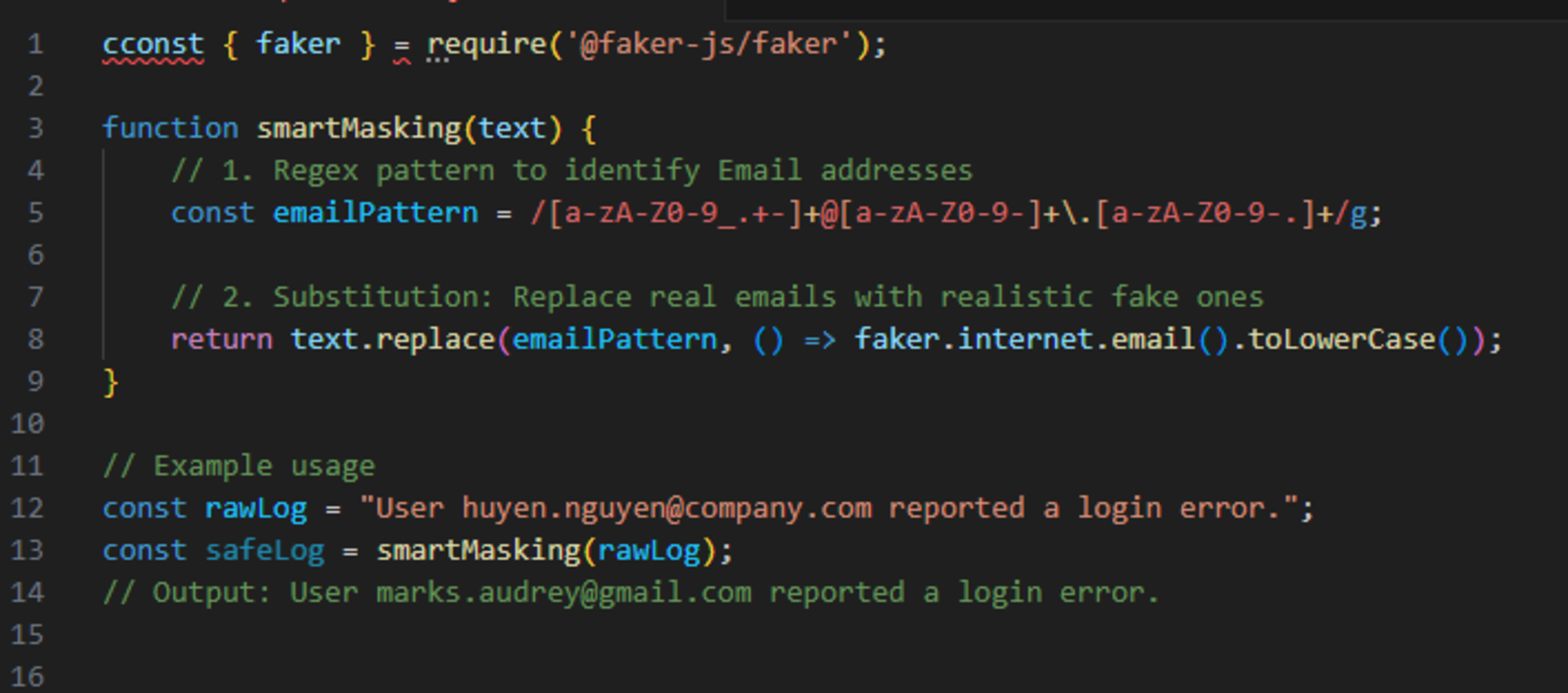
B. For Tech Staff - Automation
Developers can use Regex or libraries like Faker (Python/JS) to clean error logs before querying AI. Here is a quick example:
5. Static vs. Dynamic Masking
AWS defines two main types of masking:
- Static Data Masking (SDM): Masking a fixed set of data before it is stored or shared. Ideal for creating Testing environments.
- Dynamic Data Masking (DDM): Masking data in real-time as it is queried. Perfect for Customer Support systems where access is based on user roles.
Conclusion
Think of an AI chat box like a stranger on the street. Would you shout your bank password to them? If not, don't paste it into AI without masking it first.
At ISB VIETNAM, we follow strict security standards to ensure your code and data are always safe. Are you looking for a trusted outsourcing partner with professional security workflows?
[Contact ISB VIETNAM today for a secure software solution!]
Or click here to explore more ISB Vietnam's case studies
Have you ever accidentally pasted sensitive data into AI? Let us know in the comments how you handled it!
References
https://aws.amazon.com/what-is/data-masking/
https://www.linkedin.com/pulse/6-types-data-you-should-never-mention-ai-mekari-4timc
Image from Gemini
